There are many good guides on the internet on how to use and configure Cloudflare Tunnels, Traefik, and Let’s Encrypt, using wildcard certificates, and Cloudflare Access, for authenticated home lab network access. This is yet another such guide, but using a single wildcard subdomain for remote homelab access. An advantage of using a wildcard subdomainContinue reading “Yet Another Cloudflare Traefik Let’s Encrypt Guide”
Category Archives: solution
Halloween pumpkins and lights
Last year was the first time I used RGB holiday lights for decorative outside lights, and this year Halloween I started with some Halloween pumpkins. I used a Boscoyo Pumpkin King and a Goofy Gourd because they are printed in color so they look good day and night. The Pumpkin King stands 95″ / 2.4mContinue reading “Halloween pumpkins and lights”
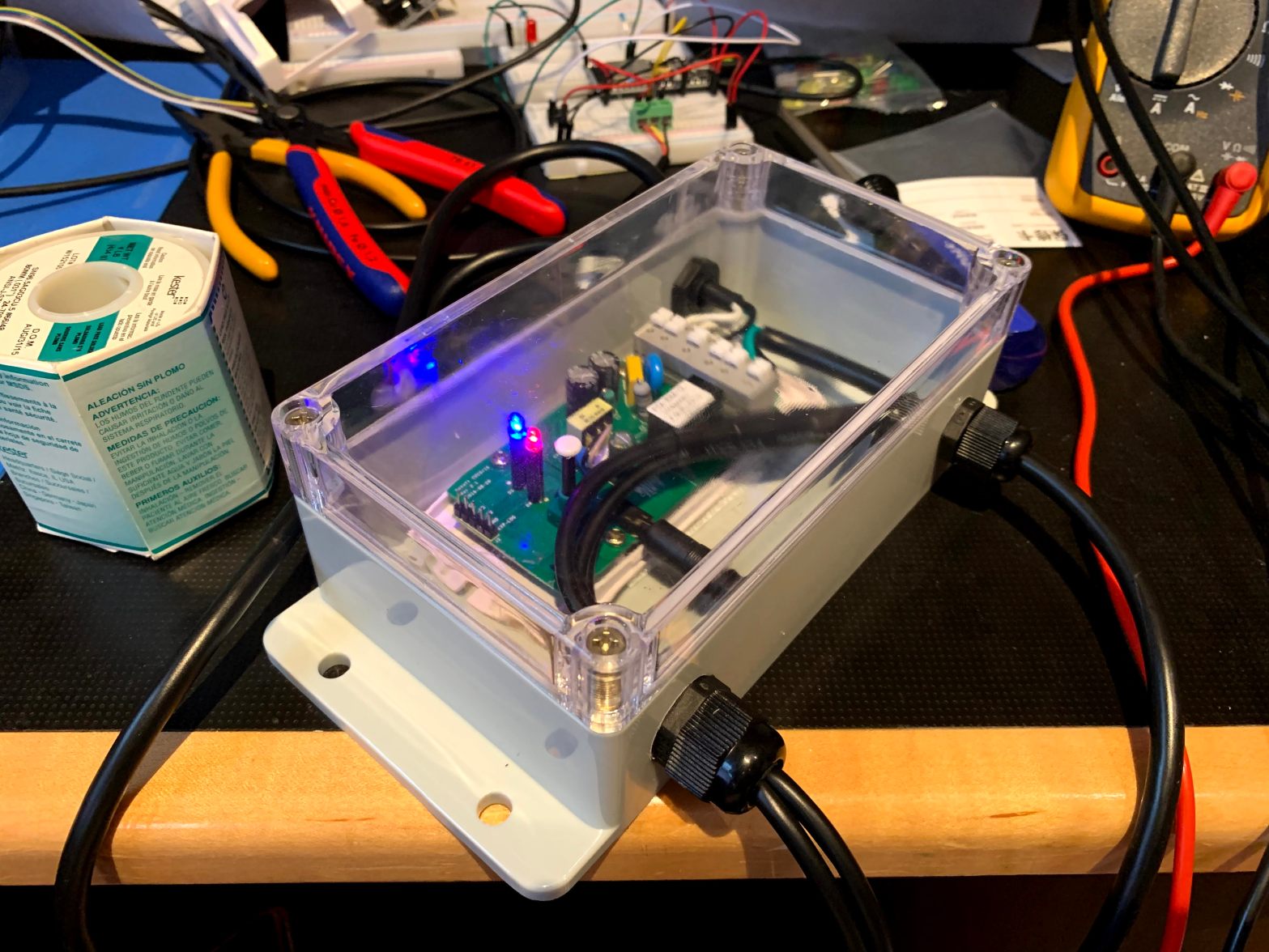
Hot Water Recirculation Pump Controller
Our house uses a Noritz natural gas instant hot water heater, with a dedicated hot water recirculation line. Problem is the heater is installed in the garage, and in the summer the the garage gets so hot that the aquastat that controls the recirculation pump never turns on. This leaves us with cold water inContinue reading “Hot Water Recirculation Pump Controller”
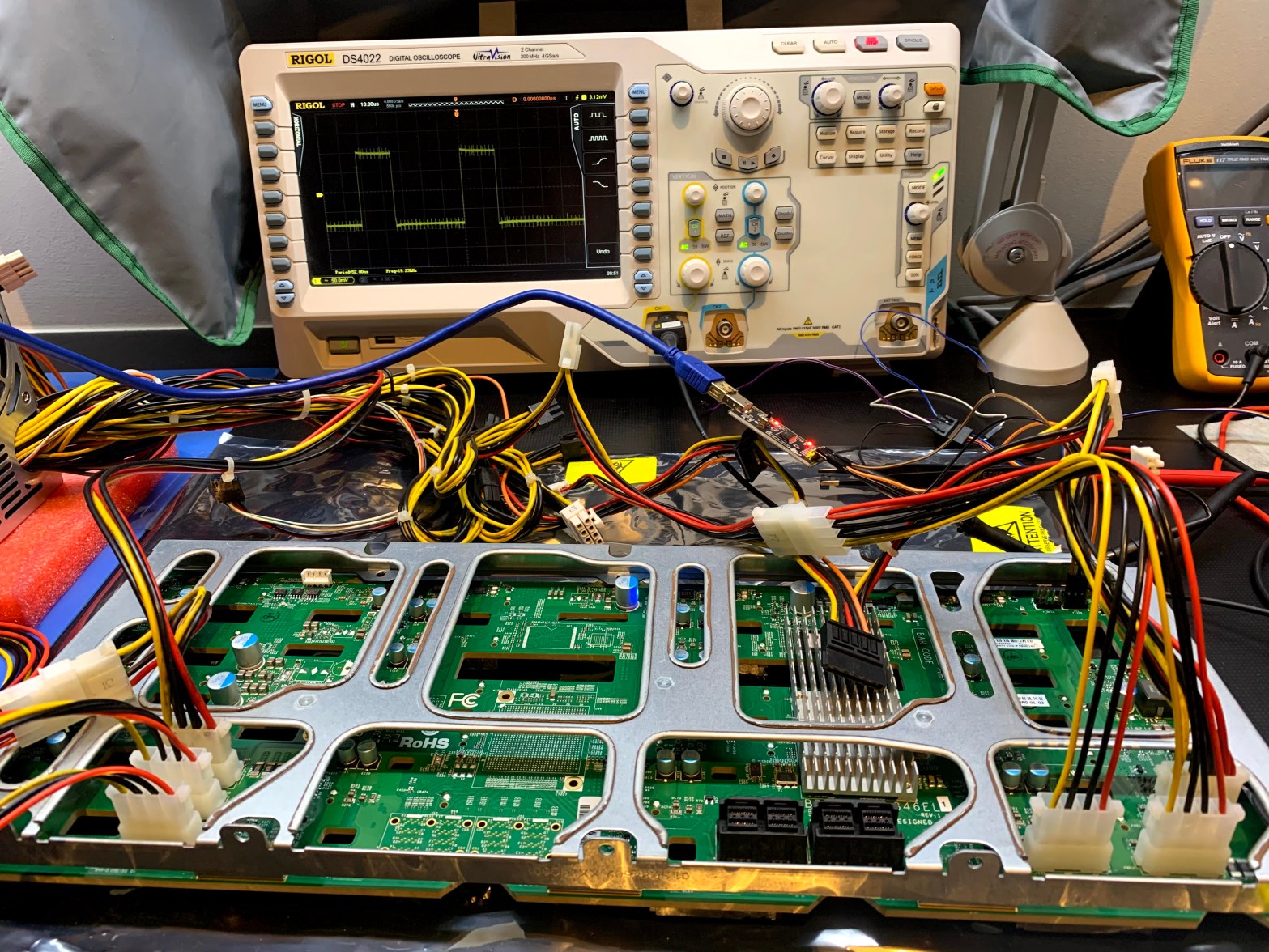
Recovering the Firmware on a Supermicro BPN-SAS3-846EL1 Backplane
In a previous adventure I replaced an Adaptec HBA with a LSI SAS3 HBA, and the chassis drive bay LED’s stopped working. I suspect the LSI card does not play nice with the SGPIO sideband controller, and I decided to replace the chassis with one similar to my SC846 chassis, where the LSI card andContinue reading “Recovering the Firmware on a Supermicro BPN-SAS3-846EL1 Backplane”
Unraid and Robocopy Problems
In my last post I described how I converted one of my W2K16 servers to Unraid, and how I am preparing for conversion of the second server. As I’ve been copying all my data from W2K16 to Unraid, I discovered some interesting discrepancies between W2K16 SMB and Unraid SMB. I use robocopy to mirror filesContinue reading “Unraid and Robocopy Problems”
eNom Dynamic DNS Update Problems
Update: On 27 July 2018 eNom support notified me by email that the issue is resolved. I tested it, and all is back to normal with DNS-O-Matic. Sometime between 12 May 2018 and 24 May 2018 the eNom dynamic DNS update mechanism stopped working. I use the very convenient DNS-O-Matic dynamic DNS update service toContinue reading “eNom Dynamic DNS Update Problems”
Circumventing ThinkPad’s WiFi Card Whitelisting
What started as a simple Mini PCI Express WiFi card swap on a ThinkPad T61 notebook, turned into deploying a custom BIOS in order to get the card to work. I love ThinkPad notebooks, they are workhorses that keep on going and going. I always keep my older models around for testing, and one ofContinue reading “Circumventing ThinkPad’s WiFi Card Whitelisting”
Self Signed BitFury Drivers
Almost two years ago I pre-ordered some bitcoin mining hardware from Butterfly Labs, what a waste. After countless delays, more than a year late, they finally shipped the hardware, and given the low probability of ever recovering the money through mining, I immediately sold the hardware on eBay, for a little profit. In the mean time USB stickContinue reading “Self Signed BitFury Drivers”
Windows 8 VIDEO_TDR_FAILURE Madness
I finally figured out why I kept on getting VIDEO_TDR_FAILURE BSOD’s when installing Windows 8 on my SuperMicro workstations. It turns out that the problem goes away when I use a PCIe slot associated with CPU #1, instead of a slot associated with CPU #2. Some history on my adventures with Windows 8 and SuperMicroContinue reading “Windows 8 VIDEO_TDR_FAILURE Madness”
WordPress.com 404 With Blogger Permalinks
Part of the research I did before migrating from Blogger to WordPress.com, was to make sure that current Blogger permalinks will resolve correctly once the old posts were imported into WordPress.com. At the time all seemed fine, but soon after migrating, I received alerts from Google Webmaster Tools that there is an increase in siteContinue reading “WordPress.com 404 With Blogger Permalinks”

You must be logged in to post a comment.